The Global Risks Report is published by the World Economic Forum and presents the major risks the world will be facing in the coming year. I’ve been following this report for years especially because of the evolution of cybersecurity. The concept of “cyberattacks” has been part of the Global Risk Report for the last 9 years and has been evolving since then.
The 2020 report includes the top ten types of data fraud and cyberattacks in terms of likelihood and infrastructure breakdown and the top ten types of cyberattacks in terms of their impact.
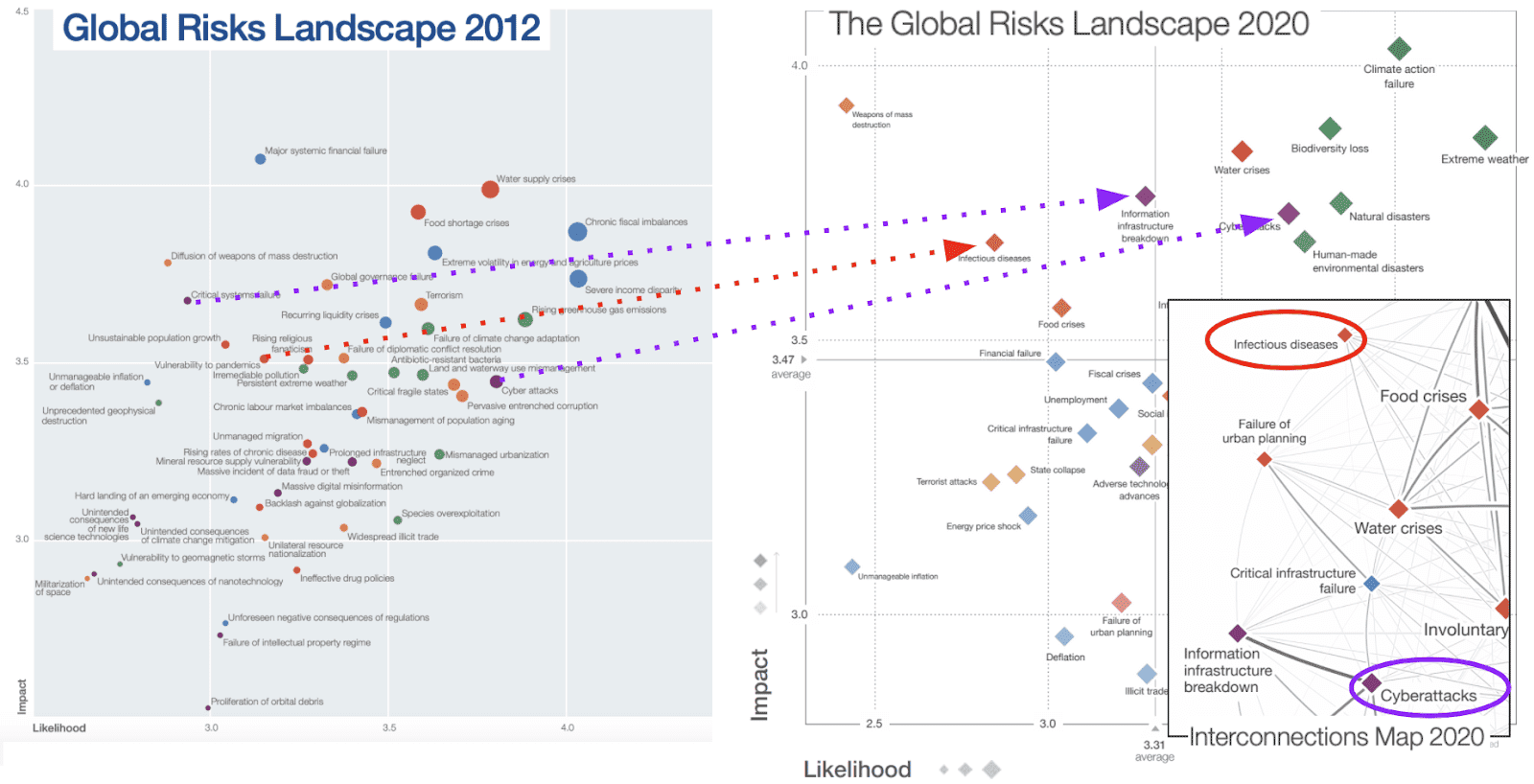
Although pandemics and infectious diseases have been losing impact and likelihood over the years, this is not the case with the current COVID situation.
Another important aspect of this report is how risks are interrelated with each other. Pandemics and infectious diseases seem to have a very low relation to cyberattacks.
However, in the case of COVID, it has brought about a number of changes in how we work and live, all of which are susceptible to the threat of hackers. Examples of these changes include:
- The number of remote workers will increase. There are many countries under 100% quarantine, and this impacts how employees are able to work.
- Special roles that require local access are being adapted through changes in security policies.
- Internet traffic consumption is increasing and this may bring service restrictions. Netflix and Amazon have already announced that they will decrease the video quality for Europe.
- Applications impacted by critical processes must be available remotely
- Critical company information will be spread out amongst those working remotely.
The following graph from the Global Risk Reports shows the evolution of risks between 2012 and 2020. The latest interconnections map, which shows the interrelationship of these risks.
The American Cybersecurity and Infrastructure Security Agency (CISA) agency has released an article that describes cybersecurity considerations for remote workers and recommendations for companies:
- VPNs are key for these scenarios, it is critical that we as a company check that our solutions have been updated and patched to avoid known vulnerabilities of the solutions
- Phishing is expecting to increase to steal usernames and passwords from remote workers.
- Additional security for VPNs, such as double factor authentication and policies that control the number of concurrent VPN connections, countries, and times, will be key to supplement security.
From my experience with customers, there are extra considerations that we should consider. These include:
- Listen to your users. Threats via email and WhatsApp will increase. We need to provide simple mechanisms for reporting security concerns.
- Allow remote access only through security protocols. There are a lot of customers who still allow RDP for remote workers. Unsecure protocols should be allowed only through VPN or virtualized environments.
- If you don’t have a Bring-your-own-device (BYOD) policy, you should have a way to enforce the use of corporate devices for company applications/information. The limit between corporate and personal devices might look weaker for remote workers, and we need to be able to control it. There will be a challenge to provide traceability, confidentiality, and integrity in non-corporate devices.
- The use of public WiFis should be restricted. Public WiFis is exposed to different hacking techniques such as man-in-the-middle (MITM) attacks, Domain Name Server (DNS) hijacking, etc.
- DNS security is key. Tech Accord published an article this week that describes the different DNS related risks. Vulnerabilities within DNS can allow cybercriminals to change the authoritative DNS and redirect users to malicious sites, apps or to intercept email.
- Assuming multi-factor authentication (MFA) is in place, there may still be ways to avoid this, like a password recovery link. We really need to manage these safety measures.
From my personal point of view, cyberattacks are an interrelated risk of the current COVID crisis and we need to consider these risks for remote workers.





